Stepper Files
As you are surely aware, the Glowforge does not use G-Code. The cloud software sends instructions to the device packaged as a proprietary binary file. The file itself is fairly simple, and contains two main sections: the header and the motion/laser commands.
Header
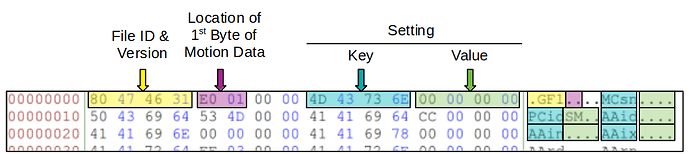
The header begins with 0x80, followed by the ASCII characters GF, and the number 1. It is assumed that 1 specifies the version of the file.
The next two bytes provide the address of the first byte of motion data. The LSB is first, so the value in the example above is 0x01E0.
This is followed by a sequence of key/value pairs that provide settings information for the device. The key’s are four characters long, and the values are contained in the next for bytes beginning with the LSB. Most of the keys have yet to be deciphered, but you can find a list of the ones that have been seen in the wild (along with possible descriptions - scroll down to “MOTION_SETTINGS”) here.
Motion/Laser Commands
The motion and laser command section of the file begins at the address specified in the header (0x01E0 in this example). Each command is exactly one byte, and is executed at a set rate called the step frequency. The step frequency is set in the header by the key/value pair STfr. This is typically set at 10 kHz, meaning they are executed at a rate of 10,000 commands per second.
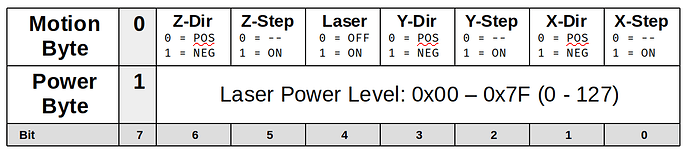
Each command can either be a motion byte or a power byte, and are encoded as follows:
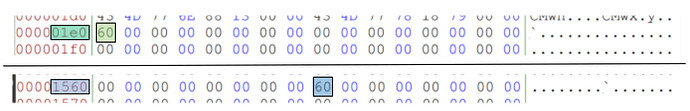
Continuing with our example, we can see the first command is located at 0x01E0, as specified in the header, and contains the command value 0x60:
In binary, this value is 0b01100000, giving us a step of the Z-Axis in the negative direction. The next 0x1388 (5,000) bytes are zero-filled (0.5 seconds), followed by another negative Z step.
Power bytes set the power that the laser will fire at when a motion byte with the Laser On bit (4) is executed.
The Glowforge Utilities package contains some rudimentary methods for interacting with these command files, as well as some sample files to tinker with.
H/T to @palmercr who did the bulk of the discovery on these files.